//Kevin Anderson /April 5 / 2013
Using photo data to verify images on Flickr and Google+
On New Year’s Eve 2012 and the first day of 2013, Facebook users uploaded 1.1 bn photos. That’s just one indication of the size of the user-generated content revolution. In the first of our series looking at UGCUGC (User-Generated Content)Content created by the public at large, generally not professionally edited,…//read more , we began looking at how to find the images that you want, and can use, with a focus on the photo-sharing site Flickr.
However, as journalists, the first question that we ourselves ask after finding an image is how to verify it. Fortunately, Flickr and other photo-sharing sites, including the photo sharing feature on Google+, provide a lot of information that will help you authenticate the photos you find.
Verifying the authenticity of a photo
In the last article, we looked at a photo that was reportedly taken in Japan after the earthquake and tsunami in 2011 by the US Navy.
But how do we know that the US Navy actually took this photo? How do we verify the location? Almost all digital cameras, including camera phones or smartphones, save a wealth of data along with the image. Smartphones, and some point-and-shoot cameras with GPS receivers, also include the location of the photo in this data. This information is created and stored with the image as EXIF (Exchangeable Image File) data.
One of the benefits of Flickr is that it retains all of the data created by the camera that shot the photo. This data will tell you the date, the camera settings and whether the photo was opened in photo editing software. Sometimes it will also tell you the location of the photo, either by place name or, occasionally but especially if the photo was taken with a smartphone, the GPS coordinates. To access this information, clickClickA click can denote several different things. It can be a metric that…//read more on Actions in the menu above the photo and from the drop down menu select View EXIF info:

This will show you all of the information associated with photo. In this case, it tells you not only a lot about the camera, but also that the photo was taken by “Mass Communication Specialist 3rd Class Alexander Tidd” who is assigned to the US aircraft carrier Ronald Reagan. Additionally, it tells us that the photo was opened in Photoshop. With this information, you can have a lot of confidence about the sourcing of this information and, if in doubt, you could always call the US Navy press office to confirm the details.
What about the location? That requires a bit more thought. If you look to the right of the photo, you’ll notice a map, which you can enlarge by clicking on it. You’ll also see that the dateline of the photo is Wakuya, but the map clearly shows that this photo cannot be from there because that city is landlocked, not on the coast. So the photo is probably another city in the same area; they simply used the name of a major city in the area for convenience.

How much should you trust location information on Flickr? It depends on how the information was recorded. With this photo, the location was either added manually, or, more likely, Flickr interpreted the location based on the city named in the EXIF data.
For some photos, such as this photo I took in the mountains of Colorado, the location actually comes from the GPS data from my camera phone. If you look at the EXIF information, you’ll see this:
GPS Version ID 2.2.0.0
GPS Latitude 37 deg 29′ 46.19″ N
GPS Longitude 106 deg 51′ 33.01″ W
GPS Altitude Ref Above Sea Level
GPS Altitude 3445.5 m
That information was recorded by an old camera phone, a Nokia N82. It not only recorded incredibly precise coordinates but also the elevation of the mountain ridge I was walking along. You can have a high degree of confidence in the location if the GPS information is embedded in the photo file itself. Yes, I could have added that information myself, but it is highly unlikely.
It also demonstrates that if you’re taking pictures where you might not want to divulge the exact location, you’ll want to make sure you disable all location features on your phone or camera.
For Flickr, here are a few quick rules for verification:
- Look for date and camera information. If that isn’t there, either the Flickr user doesn’t allow the EXIF information to be seen publicly, the photo has been scanned or the photo has been downloaded from another site and uploaded to Flickr.
- For photos with date or camera information, look at the EXIF data. This will often have information that shows the real source of the photo.
For instance, the EXIF data on this photo from Libya shows that someone has taken a Reuters photo and uploaded it to their own Flickr account. Although they have uploaded this under a Creative Commons licence, you cannot use it unless you pay Reuters.
On this photo of a volcano in Indonesia, the EXIF information only states:
| X-Resolution | 1 |
|---|---|
| Y-Resolution | 1 |
That’s a good indication that the photo has been downloaded from elsewhere on the internet and then uploaded to Flickr. In the next in our series on UGC, we’ll look at how you can find the likely original source of the photo.
Fortunately, Flickr isn’t the only photo-sharing service that preserves the EXIF data for photos. Google+ does as well, although photos are just one of its offerings, and not all photos on Google+ are available publicly. Just as with Flickr, Google+ users can licence their photos with a Creative Commons licence and you can search for photos that you can use commercially. That’s best done through Google image search, which we’ll cover in next article in our series.
To see the EXIF information on a photo on Google+, click on the photo to bring up more information. To the right of the photo, click on the option Photo Details. That will show you a map if the photo has location information embedded in it, and below the map, you will see any EXIF data.

Reading EXIF data on any photo
Unfortunately, most social networks strip photos of their EXIF information, and often when an image is posted to the web, EXIF data is stripped out to make the image file as small as possible. However, if you want to see if EXIF information remains on any photo, on the web or on your desktop, then there are browserBrowserA software program that can request, download, cache and display documents…//read more plugins and viewers that will show what EXIF data is available.
There are apps and plugins for Chrome, Safari and Firefox, which will work on any computer.
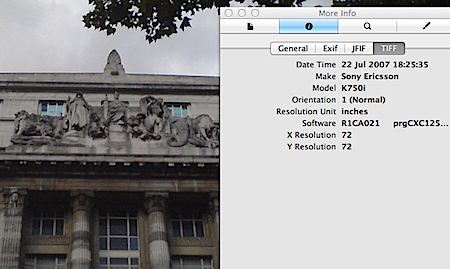
If you’re a Mac owner, you have a couple of extra options. You can use the built-in Preview application to see all of the data about an image, including the camera that took it. If you don’t see the More Info window, go to Tools and make sure that the Inspector isn’t hidden.
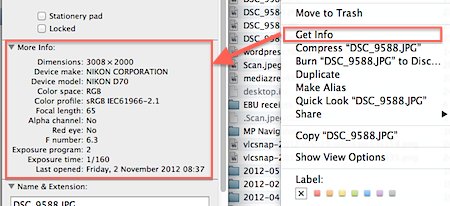
On a Mac, you can also view the EXIF data simply through the file information viewer. Do this by right-clicking, using command-I, or holding down Ctrl and clicking then selecting Get Info. This will show you all of the information about any file in your system including an image file.
Another important verification option: Contacting the photographer
Knowing the camera that took a photo can be an important piece of information. If someone has sent you a photo via a mobile phone, you have their mobile phone number. If they took the picture with the phone, you hopefully also have some EXIF information. At a conference I once attended, a member of CNN’s UGC team, iReport, said that they would contact the photographer and simply ask them what kind of camera they took the photo with. If they couldn’t answer or if they answered incorrectly based on the EXIF information, then that automatically raised other questions.
UGC teams at major news organisations and also UGC news service Storyful have developed these techniques as the volume of content and the use of user-generated content has exploded. EXIF data is just one tool of their trade to make sure that the photos they use are authentic. In the next of our series, we’ll look at how image search services can help you uncover hoax photos.
Article by Kevin Anderson

Leave your comment